A conversation in Birmingham: A story based on true events
Once upon a time in a cloudy and chilly winter day in Birmingham, a conversation between hemo and Mr. X took a place. A conversation about network emulators and how important they are.
Act 1: The conversation
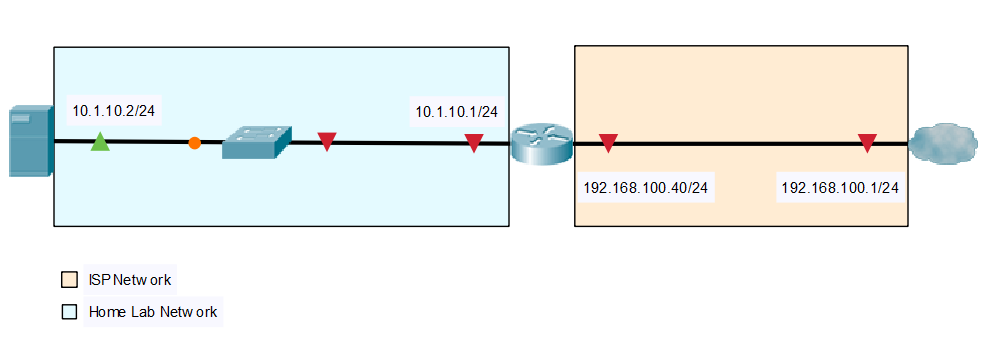
Mr. X: There are multiple network emulators that can be run on Type 2 hypervisors like GNS3 that runs on VMware Workstation and VirtualBox and EVE-NG that execlusively run on VMware Workstation .
Hemo: I think you are wrong regarding the inability of running EVE-NG on Oracle VirtualBox.
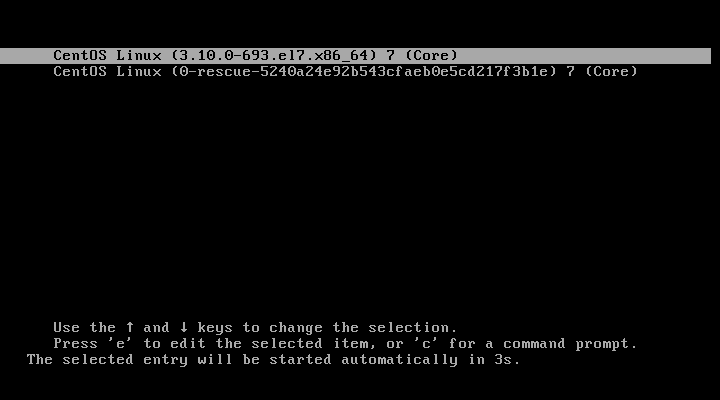
Mr. X: I have tried to run EVE-NG on VirtualBox multiple times before. Unfortunatly, It keeps crashing on boot. I even tried installing it from the ISO file. It kept crashing!
Hemo: The emulator can be run on VirtualBox, but it requires certain tweaking to run properly. The reason behind that is that it requires nested virtualization which was not supported by VirtualBox until recently and it is disabled by default.
Mr. X: This is wonderful! I always thought it is not possible to run it on VirtualBox. So, how do I run it on VirtualBox?
The light turned off ending the first act.
Act 2: The guideline
Requirements
Running EVE-NG on VirtualBox requires certain requirements. First, CPU virtualisation support needs to be enabled on the BIOS. Second, the latest version of VirtualBox is installed. Lastly, there are certain specification needs to the host machine to have like the host has at least 4 GB memory, 40 GB of free storage space and a fairly good performance like AMD Ryzen 5 or Intel Core i5 processors or higher.
Downloading EVE-NG and its companion component
EVE-NG comes in two flavours; paid and free. However, In this post we will stick with the free edition a.k.a the communicaty edition. Yet, the instructions can be the similar if not identical for both versions. To download EVE-NG go to EVE-NG official website.
In the home page go to downloads. The home page looks like the image below.
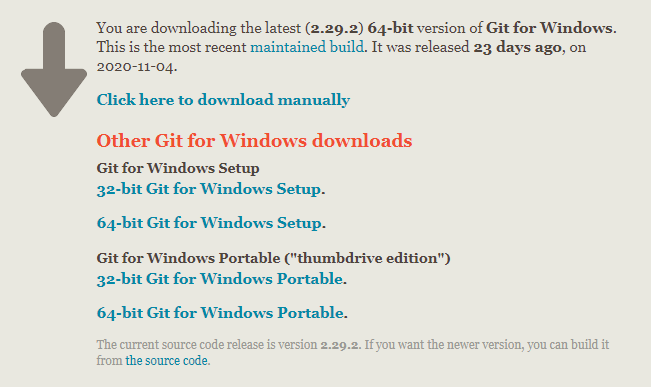
In the download page, select the OVF version of the community edition. EVE-NG provides two methods to download the emulator; MEGA link and Google Drive link. Select one of these links.
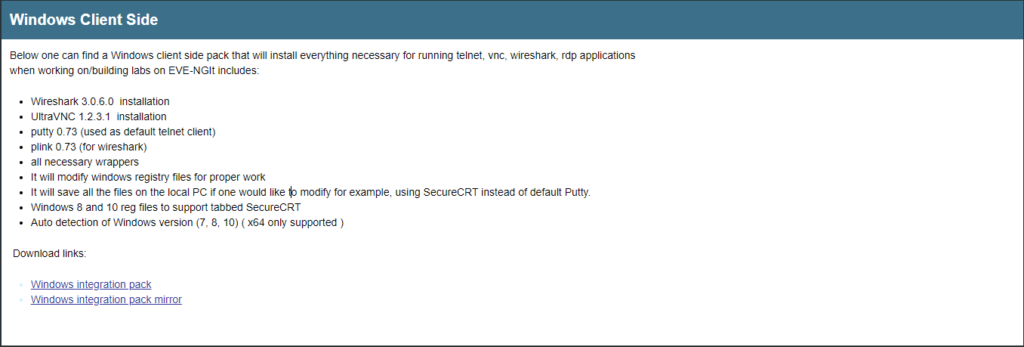
Integration pack is a companion component that works along with EVE-NG birnaries. The companion components consists of different tools like putty and wireshark wrapper and it aims to improve user experience. Integration pack supports Windows and Mac OSX (Intel / M1 processor). To download to the companion scroll down and click on integration pack that matches the platform you are using. The image below shows the link to download the pack for Microsoft Window platform.
Once the OVF is downloaded, extract the compressed file and keep it in a known location.
Importing OVF
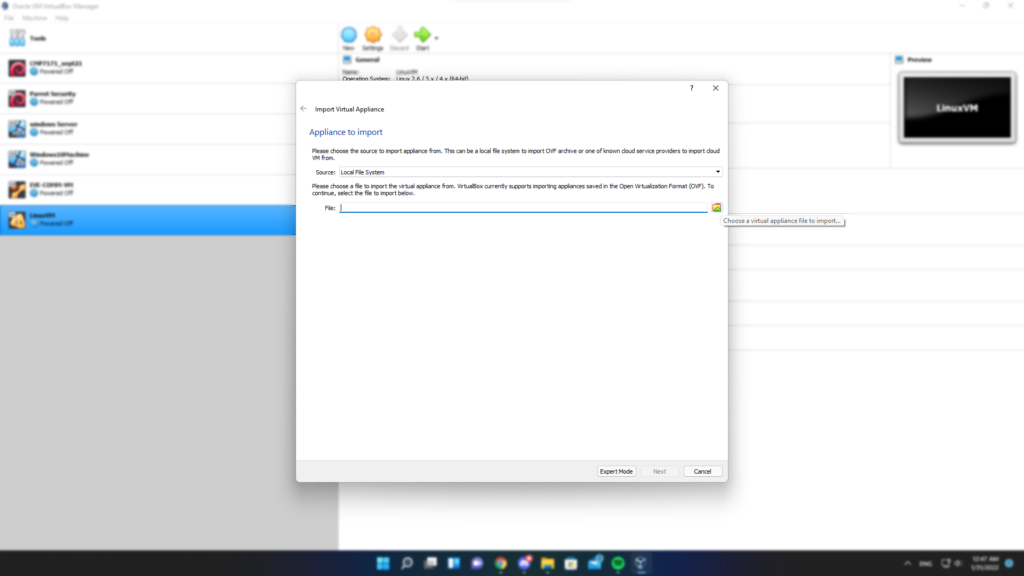
The second step after downloading and extracting the required files is importing OVF into VirtualBox. Open VirtualBox and click on File ->Import Appliance from top menu as in the figure below.

Navigate to the prevoiusly extracted EVE-NG compressed file, select and OVF files and click Next.
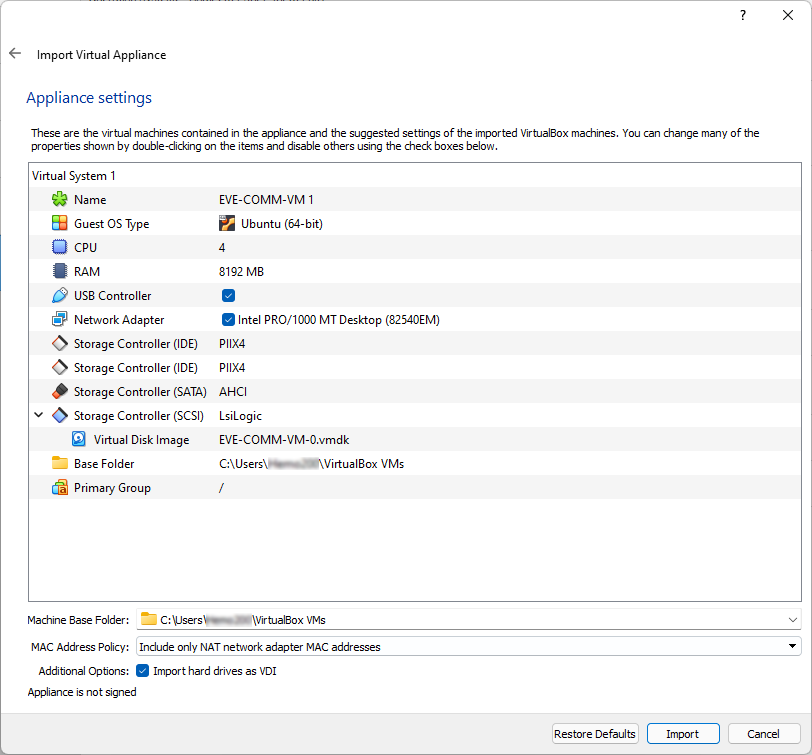
In the next window keep setting at default and click Import
Configuring the EVE-NG for VirtualBox
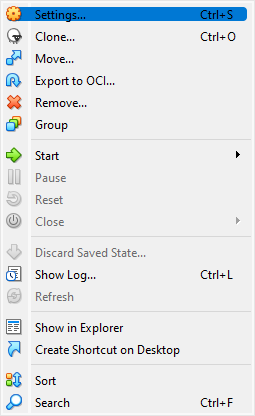
The next step is configuring the appliance for VirtualBox. Right click the recently imported appliance and click Settings.
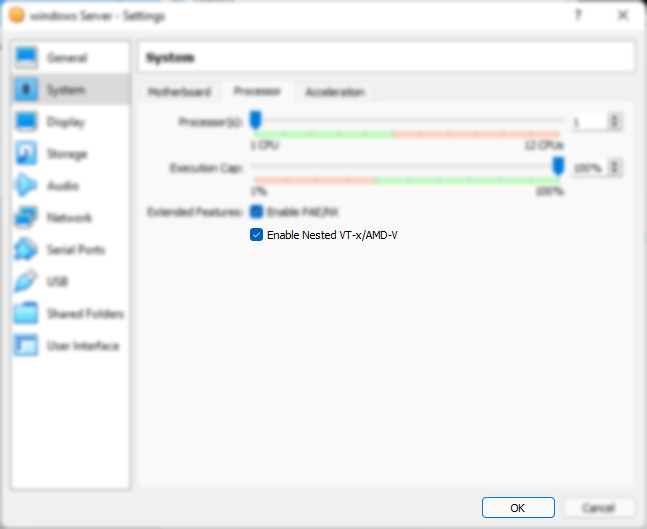
Next, Click on System and then click on Processor. You will notice that Enable Nested VT-x/AMD-V is not enabled. As a result, EVE-NG is failing to boot. To mitigate this issue, tick the box as in the image below and click OK. Not enabling Nested virtualisation is the main cause of EVE-NG failing to boot.
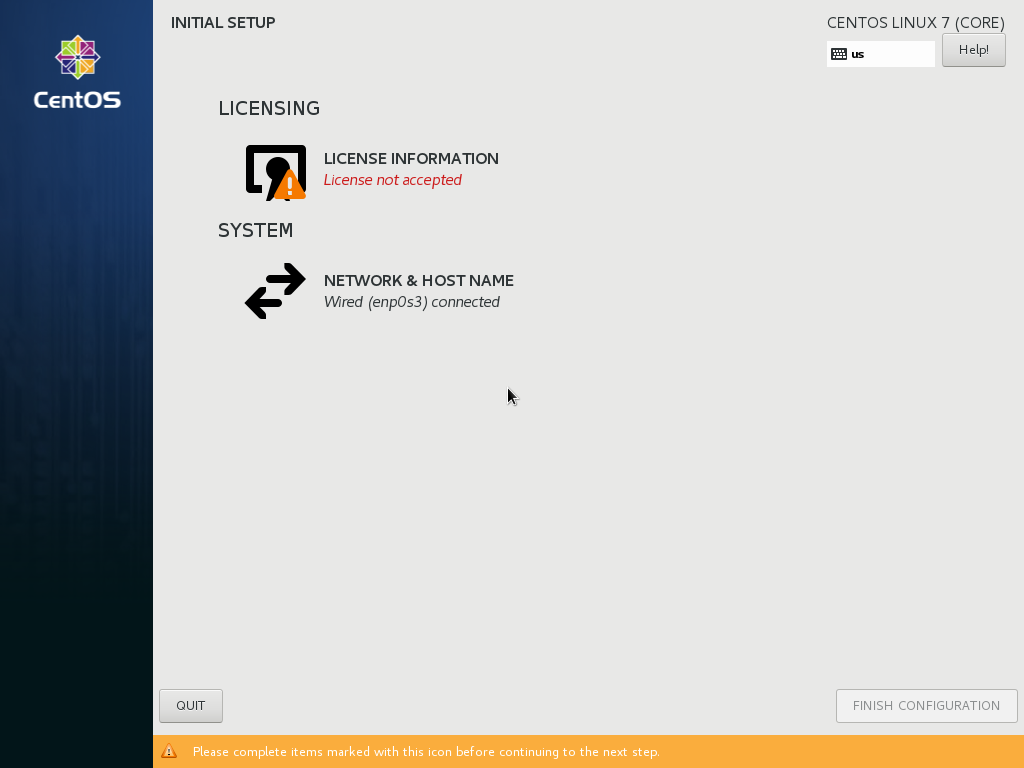
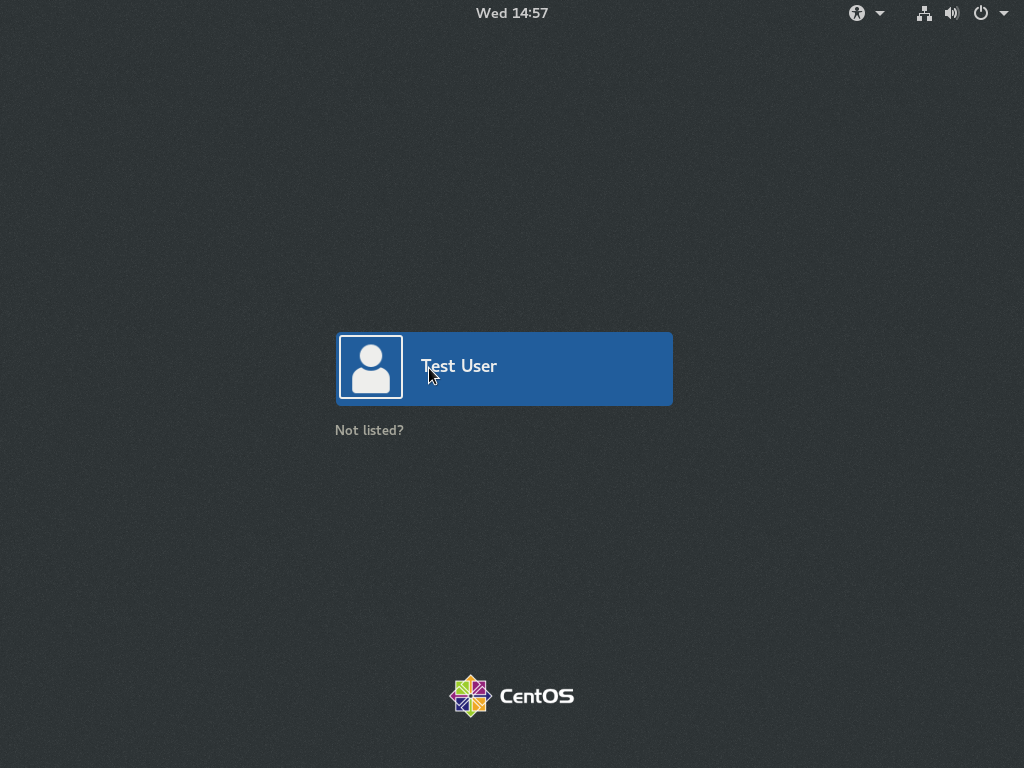
Go back to VirtualBox and click on Turn On EVE-NG virtual machine. Once the VM is turned on check VM console window. The VM console window displays the IP address that is assinged to the virtual machine.
Accessing EVE-NG
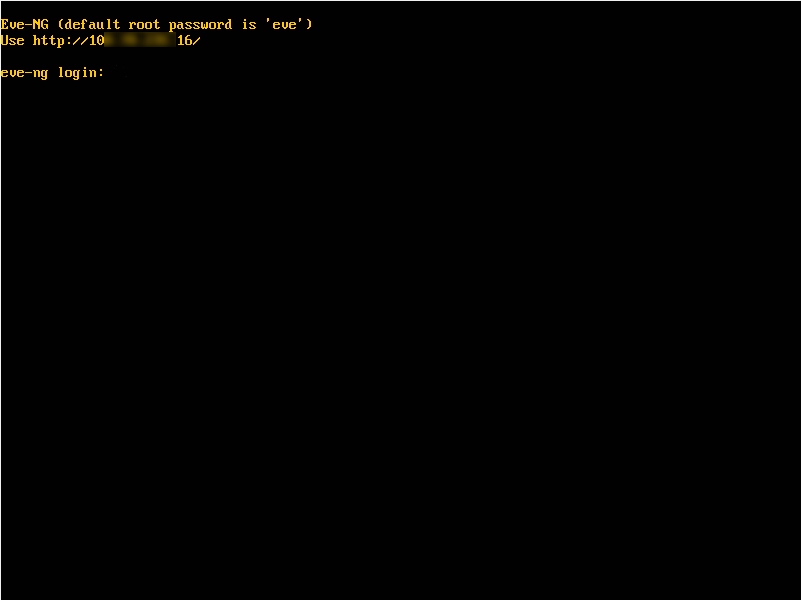
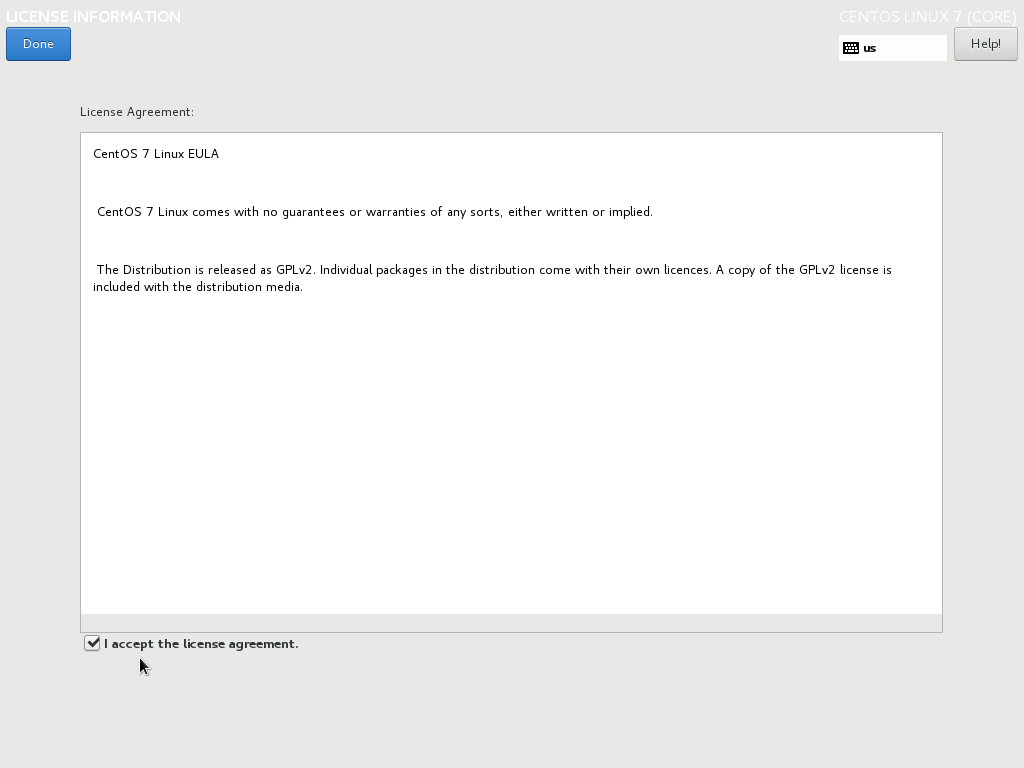
Finally, open a browser and type the same IP address displayed in EVE-NG console page. The browser should display a similar output to the image below.

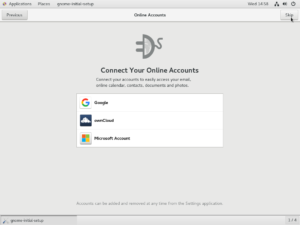
Companion pack installation
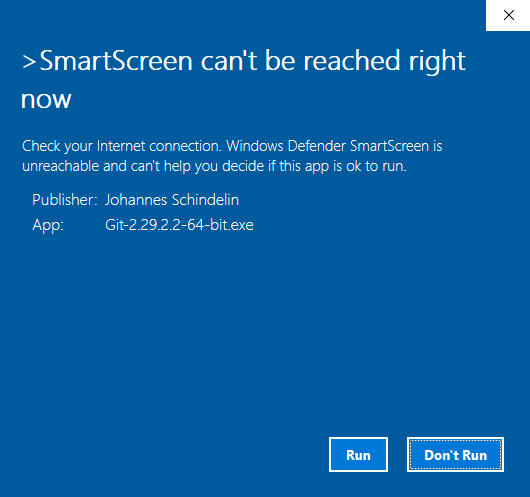
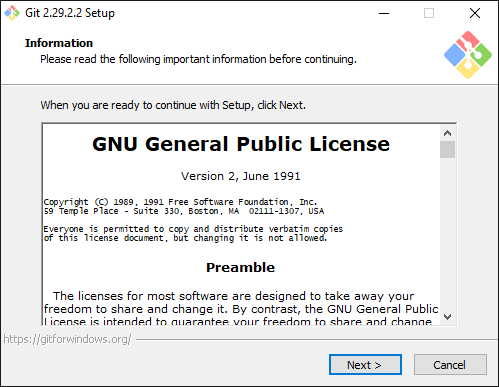
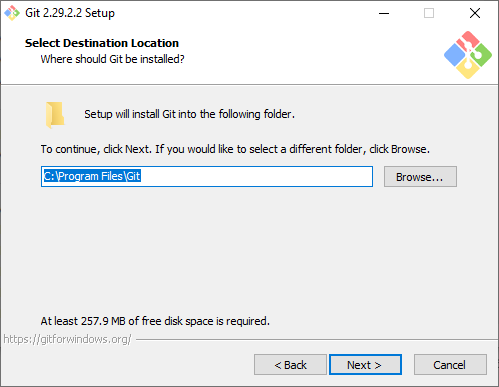
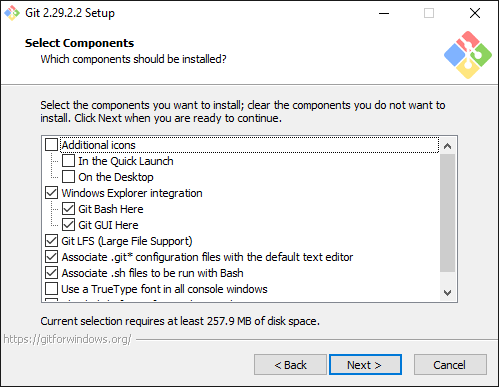
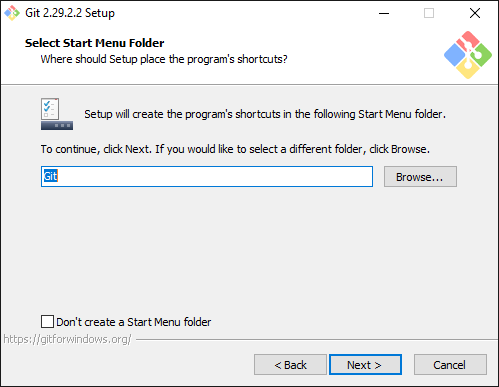
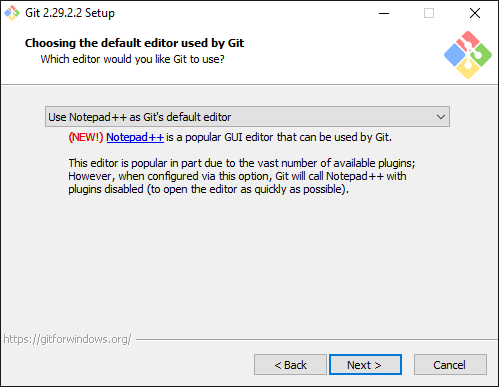
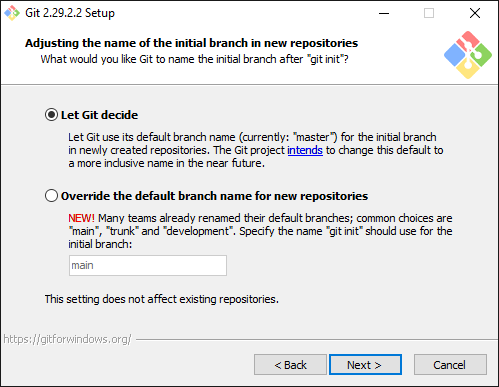
Finally, After successfully running the emulator we shift gears and install the companion pack. It starts by double clicking on downloaded file. Then, keep all setting on default and keep click on Next until the end of the wizard.